Minimizing Risks by Minimizing Exposure in Apps
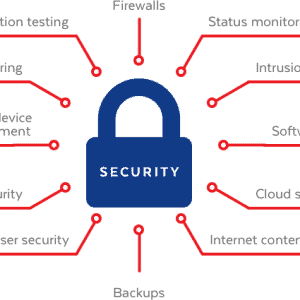
When it comes to security for small business owners, it’s not a matter of if, but when your information or apps will be compromised. Malicious hackers are on the rise. Both large companies and small businesses are trying to keep up by updating apps, applying software patches, and using cloud-based applications. Losing customer data usually spells disaster—if your apps or systems leak tax records, contracts, or confidential data, your business reputation will suffer.
Cybersecurity goes beyond hackers—natural disasters can also impact your apps and data. An eight-person law firm in Miami lost everything to Hurricane Ike in 2008. With a proactive approach to app and data backup, they could have survived. Today, cloud apps and backup solutions help companies protect sensitive data. More businesses now invest in app security and data protection.
Continuing Business Continuity in the Face of Disaster
Many small businesses overlook app security and business continuity. Here are some common misconceptions about app and data security:
Mistake 1: “My data is secure since it’s backed up on the premises.” Backing up apps and data in your physical office is not enough. If disaster strikes, you could lose everything. Use trusted third-party apps or cloud solutions for off-site backups. With the right apps, employees can securely access data from anywhere.
Mistake 2: “I have the latest PC, so I’m protected from security issues.” New hardware doesn’t guarantee app security. You need to update all your apps, install firewalls, and use robust antivirus software. Protect both your computers and your network routers. Secure all endpoints, not just the main PC.
Mistake 3: “I’ve installed new security protections in the past couple of years, so I’m good.” Over 6,000 new computer viruses are released every month. Outdated apps and expired antivirus programs leave your business exposed. Replace free trials with professional security apps that protect both files and applications.
Update Your Browser and Operating System for App Security
Major operating systems and browsers release security patches often. If you don’t update your software and apps, you risk falling victim to viruses or phishing. Enable automatic updates for your apps, browser, and operating system. This way, your software tools stay protected without extra effort.
Internal Security Issues with Apps
Most attacks come from outside, but internal threats to apps and data are also serious. As your business uses more mobile apps and devices, risks increase. Employees, dealers, or partners may gain unauthorized access to apps or data storage. If you ignore these risks, you put your assets and reputation in danger.
Portable devices: Employees use phones, tablets, and external drives to access apps and files. These devices are often unregistered, making it hard to track uploads and downloads. Secure all mobile apps and require users to follow company policies, especially when working off-site.
Keep all security apps and antivirus software updated. Outdated security apps can’t protect your network or mobile devices from new threats.
Avoid using public Wi-Fi for business apps. Open networks in airports, hotels, or restaurants are not secure. Hackers can intercept data sent through your apps on these networks.
Watch out for email attachments. Phishing emails often look real but try to steal your information. Use security apps that scan all incoming and outgoing emails for malware.
Peer-to-peer file sharing apps open ports that can let in viruses or spyware. Limit their use and always scan files before opening.
Disgruntled employees: Sometimes, former employees with access to apps or sensitive data might act out of spite. Always update app permissions and remove access before letting someone go.
System administrators must maintain and monitor app security. Poorly trained IT staff can create risks if they don’t understand the latest app security procedures. Make sure your IT team is certified and up to date.
In our experience, apps and data issues are best solved with help from professionals like the Florida Nerds. Since 1994, Florida Nerds has provided expert computer repairs, app support, and IT security in the tri-state area.